Overview of Distributed Systems: Characteristics, Classification, Computation, Communication, and Fault Models
Characterizing Distributed Systems: Multiple autonomous computers with CPUs, memory, storage, and I/O paths, interconnected geographically, shared state, global invariants. Classifying Distributed Systems: Based on synchrony, communication medium, fault models like crash and Byzantine failures. Comp
9 views • 126 slides
Understanding Hash Maps: A Common Data Structure
In this module, learn about Hash Maps, a common data structure used in various programming languages like Java, C#, C++, Python, and PHP. Hash Maps allow you to store key-value pairs without duplicate keys, making it efficient for mapping relationships between data elements. Explore how to declare,
6 views • 16 slides
Quick Hash Delivery in Ottawa Canafast.ca
Craving premium hashish in Ottawa? Look no further. Our service offers prompt and discreet hash delivery right to your doorstep in Ottawa. Indulge in the finest hash products without leaving the comfort of your home.
3 views • 6 slides
If you are looking for Grazing Tables in Netley
If you are looking for Grazing Tables in Netley, Event Gourmet and Florals provide grazing tables, platters, dessert bars, cocktail food and florals for corporate functions, weddings, engagements, family events, parties and more! Whether you\u2019re hosting an event at your home, workplace, favourit
0 views • 6 slides
Weapons Training Strategies and Crew Gunnery Tables Overview
This article provides an in-depth look at the mounted machine gun gunnery gates and tables, crew gunnery progression, weapons training strategy, training gates, and crew gunnery tables. It outlines the structured approach to attaining and sustaining direct fire proficiency for various weapon systems
1 views • 16 slides
Understanding Hash Join Algorithm in Database Management Systems
In this lecture, Mohammad Hammoud explores the Hash Join algorithm, a fundamental concept in DBMS query optimization. The algorithm involves partitioning and probing phases, utilizing hash functions to efficiently join relations based on a common attribute. By understanding the intricacies of Hash J
1 views • 41 slides
Maintaining an Operating Table: Principles and Functions
An operating table system comprises three components - the table column, table top, and transporter, each available in different versions for various surgical disciplines. Stationary tables are anchored to the floor, offering flexibility to adapt to patient needs. Mobile tables provide maneuverabili
0 views • 12 slides
Importance of Times Tables and the Multiplication Tables Check for Children
Times tables play a crucial role in supporting children's mathematical foundation, essential for their future academic success. Understanding the significance of multiplication facts up to 12x12 is emphasized, aiding proficiency in later years. The Multiplication Tables Check, conducted digitally, e
1 views • 18 slides
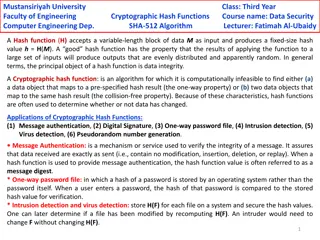
Cryptographic Hash Functions in Data Security: Mustansiriyah University Course Overview
Cryptographic hash functions play a crucial role in ensuring data integrity and security. This course at Mustansiriyah University's Faculty of Engineering covers the SHA-512 algorithm and its applications in various fields such as message authentication, digital signatures, and intrusion detection.
0 views • 6 slides
Shifting Bloom Filters at Peking University, China
Explore the innovative research on Shifting Bloom Filters conducted at Peking University, China, featuring evaluations, conclusions, background information, and insights on membership, association, and multiplicity queries. The study delves into hash functions, theoretical results, and the Shifting
1 views • 25 slides
Buy Playboy Hash Online - globaldrugsstore.com
Buy Playboy Hash Online is an Indica dominant hash that originated from Morocco where it is widely known to produce some of the best hash in the world. This hash is quite potent but very easy on the throat. It smokes incredibly smooth and has a sweet
1 views • 3 slides
Understanding Distributed Hash Tables in Peer-to-Peer Systems
Distributed Hash Tables (DHTs) are a fundamental component in organizing nodes in peer-to-peer networks. By using hash functions to assign keys to peers, DHTs enable efficient storage and retrieval of objects. Peers in a DHT are responsible for storing and managing key-value pairs, with each key bei
0 views • 31 slides
CSE 373 - Hashing Concepts and Exam Preparation
Introduction to hashing in CSE 373, covering basic concepts, hash functions, collision resolution, and runtimes. Exam details for Friday's practice exam include topics on Stacks, Queues, BigO Notation, Heaps, Trees, Design Tradeoffs, and exam format with emphasis on theoretical understanding. Lectur
0 views • 38 slides
Understanding Hash Joins and Symmetric Hash Joins in Database Queries
Hash joins and symmetric hash joins are key techniques used in database queries to efficiently access and combine data from multiple tables. Hash joins load candidate records into hash tables for quick probing, while symmetric hash joins maintain two hash tables with two hash functions. Despite thei
0 views • 8 slides
Understanding Cryptography Basics and Toolbox
Cryptography serves the goals of managing who can view data, ensuring data integrity, and verifying the origin of data. It involves dramatis personae like Alice, Bob, Eve, and Oscar. The toolbox includes hash functions, symmetric encryption, and asymmetric encryption. Hash functions play a crucial r
0 views • 32 slides
Understanding Distributed Hash Table (DHT) in Distributed Systems
In this lecture, Mohammad Hammoud discusses the concept of Distributed Hash Tables (DHT) in distributed systems, focusing on key aspects such as classes of naming, Chord DHT, node entities, key resolution algorithms, and the key resolution process in Chord. The session covers various components of D
0 views • 35 slides
Overview of Peer-to-Peer Systems and Distributed Hash Tables
The lecture discusses Peer-to-Peer (P2P) systems and Distributed Hash Tables, exploring their architecture, benefits, adoption in various areas, and examples such as BitTorrent. It covers the decentralized nature of P2P systems, the challenges they address, and the advantages they offer including hi
0 views • 56 slides
Evolution of Peer-to-Peer Networks and Distributed Hash Tables
Peer-to-peer networks and distributed hash tables have evolved significantly over the years, from the early days of ARPANET to the emergence of decentralized systems like Chord, Kelips, and Dynamo. This evolution has brought about a shift towards greater decentralization, improved scalability, and e
0 views • 39 slides
Understanding Consistent Hashing and Distributed Hash Table
Explore the concept of consistent hashing and distributed hash tables to efficiently store and retrieve web pages across multiple servers. Learn how hashing functions and algorithms can distribute data evenly, handle server additions smoothly, and minimize object relocations. Discover the benefits o
1 views • 36 slides
Understanding Overlay Networks and Distributed Hash Tables
Overlay networks are logical networks built on top of lower-layer networks, allowing for efficient data lookup and reliable communication. They come in unstructured and structured forms, with examples like Gnutella and BitTorrent. Distributed Hash Tables (DHTs) are used in real-world applications li
0 views • 45 slides
Understanding Cryptographic Hash Functions
Cryptographic hash functions play a crucial role in various aspects of security, including integrity protection, checksum generation, password hashing, digital signatures, and more. They are designed to efficiently convert input data of arbitrary length into fixed-length output, aiding in tasks like
0 views • 32 slides
Adapting Linear Hashing for Flash Memory Constrained Embedded Devices
This research explores the adaptation of linear hashing for improved data handling on flash memory-constrained embedded devices. Motivated by the increasing data collection by IoT devices, the study focuses on implementing database structures like a linear hash table for efficient data processing. T
0 views • 67 slides
Understanding Hash Functions in Data Structures
Hash functions are crucial in storing data efficiently by converting a sized amount of data into a single integer. They are used to generate hash values, hash codes, or hash sums, which serve as indexes in arrays. The hash function should be quick to compute and distribute hash addresses uniformly t
0 views • 200 slides
Understanding Distributed Ledger Technology Concepts
Distributed Ledger Technology (DLT) involves core concepts like assets, ledgers, transactions, states, conditions, and inferences. It also includes distributed ledgers, cryptographic hash functions, construction of a blockchain, consensus mechanisms like proof of work, and examples of applications s
0 views • 27 slides
Cryptographic Algorithms and Hash Collisions Overview
Explore the world of cryptographic algorithms and hash collisions. Learn about various hashing algorithms like MD5, SHA-1, SHA-256, and more. Dive into the concepts of symmetric and asymmetric key algorithms and understand the risks associated with hash collisions. Discover the implications of post-
0 views • 58 slides
Understanding Trace Tables for Algorithm Testing
Trace tables are a valuable technique used to test algorithms step by step and identify logic errors. They involve using truth tables to track variable values or conditions. This content provides insights into trace tables, correcting errors in pseudocode, using examples for variable tracking, and c
0 views • 9 slides
Distributed Computing Systems Project: Distributed Shell Implementation
Explore the concept of a Distributed Shell in the realm of distributed computing systems, where commands can be executed on remote machines with results returned to users. The project involves building a client-server setup for a Distributed Shell, incorporating functionalities like authentication,
0 views • 14 slides
Understanding the Relationship between Decisional Second-Preimage Resistance and Preimage Resistance in Cryptographic Hash Functions
This work delves into the subtle question of when Decisional Second-Preimage Resistance (SPR) implies Preimage Resistance (PRE) in hash functions. It presents a tool for enabling tight security proofs for hash-based signatures by exploring the success probability of adversaries against collision res
0 views • 25 slides
Foundations of Cryptography: Digital Signatures and Collision-Resistant Hash Functions
Foundations of Cryptography explores the construction of digital signature schemes and collision-resistant hash function families using one-way functions and safe primes. The content delves into the concept of collision-resistant hash functions and their construction from the discrete logarithm prob
0 views • 31 slides
Foundations of Cryptography: Lecture 12 - Digital Signatures and Collision-Resistant Hash Functions
The lecture covers the construction of collision-resistant hash functions from discrete log, the security behind it, and the implications for digital signature schemes. It delves into the theoretical foundations of cryptography, showcasing the interplay between one-way functions, hash functions, and
0 views • 25 slides
Understanding Peer-to-Peer Systems and Distributed Hash Tables
Explore the world of Peer-to-Peer Systems and Distributed Hash Tables through a lecture by Mike Freedman, covering topics like Napster, Gnutella, BitTorrent, and the challenges they present.
0 views • 48 slides
Understanding Data Structures and Hashing in Java
Data structures play a crucial role in organizing, iterating, adding, deleting, and searching data efficiently. Hash tables, linked lists, trees, and more are explored in this overview, highlighting their strengths and trade-offs. Hashing, collision resolution strategies, and the importance of a wel
0 views • 19 slides
Understanding Naming Systems in Distributed Systems
Entities in distributed systems are uniquely identified using names, addresses, and identifiers. Naming systems assist in name resolution and can be categorized into flat, structured, and attribute-based naming. Flat naming uses random strings as identifiers, and various mechanisms such as broadcast
0 views • 21 slides
Understanding Peer-to-Peer Systems and Distributed Hash Tables
Explore the concept of Peer-to-Peer (P2P) systems and Distributed Hash Tables (DHTs) through lectures covering topics like Napster, Gnutella, BitTorrent, Chord Lookup Service, and more. Understand the advantages and adoption of P2P systems, with examples like BitTorrent and the lookup problem in a d
0 views • 56 slides
Comprehensive Overview of CSE 373 Data Structures and Algorithms Course - Autumn 2018
This document provides detailed information about the CSE 373 Data Structures and Algorithms course in Autumn 2018, presented by Shrirang (Shri) Mare. It covers topics such as hashing, collision strategies, hash tables, design decisions, testing, and more. The content includes announcements, midterm
0 views • 25 slides
Understanding Hash Tables and Handling Collisions
This content covers the concepts of hash tables, handling collisions, and efficient implementation of dictionary operations. It explores methods like direct-access tables, converting keys to non-negative integers, and using functions to work with non-integer keys. The discussion includes approaches
0 views • 32 slides
Comprehensive Guide to Hash Tables in C++ STL: Unordered Set, Multiset, Unordered Map, and Multimap
Explore the implementation of hash tables in C++ STL using unordered_set, multiset, unordered_map, and multimap. Learn how to insert, search, and erase elements, along with practical examples like word puzzles and removing duplicates from vectors. Dive into recursive functions and efficiently manage
0 views • 6 slides
Understanding Hash Tables and Hashing Concepts in Computer Algorithms
This content delves into the concept of Hash Tables, covering topics such as the support for dictionary operations, achieving constant time through direct address tables, case studies in web server maintenance, and an exploration of hashing functions and collision avoidance. It also touches upon key
0 views • 40 slides
System of Environmental-Economic Accounting Core Tables for Water
System of Environmental-Economic Accounting (SEEA) provides core tables and accounts focusing on water accounting and other environmental aspects. The core tables offer concise and relevant information essential for deriving indicators and formulating evidence-based public policies. These tables aim
0 views • 15 slides
Ivy: A Read/Write Peer-to-Peer File System Overview
Introduction to Ivy, a read/write peer-to-peer file system designed to enable easy storage and access of remote files in a distributed manner. The presentation covers the motivation for peer-to-peer distributed file systems, challenges in designing such systems, and how Ivy addresses trust issues an
0 views • 17 slides