Information Security – Theory vs. Reality
Exploring the concept of fault attacks in hardware security, this lecture delves into the various techniques used to compromise systems through non-nominal and nominal channels, as well as the potential risks introduced by trojan horses in the IT supply chain. The discussion includes differential fa
2 views • 37 slides
Enhanced Security Considerations in IEEE 802.11-23 for UHR
The document discusses enhanced security considerations for control frames and MAC headers in IEEE 802.11-23 addressing vulnerabilities and proposing encryption/decryption methods. It highlights the need for support for security protocols in control frames and the importance of protecting MAC header
4 views • 13 slides
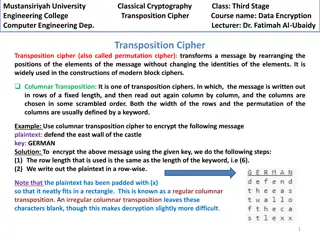
Columnar Transposition Cipher: Data Encryption Techniques at Mustansiriyah University Engineering College
Transposition ciphers, particularly the columnar transposition technique, are explored in the course "Data Encryption" at Mustansiriyah University Engineering College. The cipher involves rearranging message elements without changing their identities, making it crucial in modern block cipher designs
2 views • 4 slides
Fully Homomorphic Encryption: Foundations and Applications
Fully Homomorphic Encryption (FHE) allows computations on encrypted data without decrypting, enabling secure outsourcing of computations to untrusted servers. FHE involves key generation, encryption, homomorphic evaluation, and decryption processes. It ensures correctness, security, and compactness
3 views • 31 slides
Ciphertext Policy Attribute Based Encryption (CPABE)
Ciphertext Policy Attribute Based Encryption (CPABE) is a method that links access policies with ciphertext, allowing decryption based on user attributes rather than specific keys. This enhances security and flexibility in data access control. The encryption system also addresses challenges in remot
5 views • 26 slides
Introduction to Cryptography, Cryptanalysis, and Cryptology
Cryptography involves protecting information by encrypting and decrypting data, while cryptanalysis focuses on breaking encryption methods to access hidden messages. Cryptology encompasses both cryptography and cryptanalysis. Encryption encodes messages to prevent unauthorized access, while decrypti
8 views • 12 slides
ADFGVX Cipher: Encryption and Decryption Techniques
Discover the ADFGVX cipher, a historical encryption method used to secure messages during World War I. Learn about Fritz Nebel and Gino Painvin, who played significant roles in its development. Explore the Polybius Square invented by Polybius in the 2nd century BC for converting letters to numbers.
15 views • 14 slides
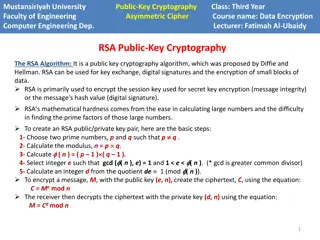
RSA Algorithm in Public-Key Cryptography
The RSA algorithm is a crucial public key cryptography method used for key exchange, digital signatures, and data encryption. It involves generating public-private key pairs using prime numbers, encryption with the public key, and decryption with the private key. The algorithm's strength lies in the
3 views • 5 slides
Effective Antivirus Approaches and Malware Defense Strategies
Antivirus approaches play a crucial role in combating malware threats. Prevention is key, followed by detection, identification, and removal of viruses. Generic Decryption technology aids in detecting complex polymorphic viruses without causing any harm to the computer. CPU emulator, virus signature
2 views • 22 slides
Hardness of Proving CCA-Security in Signed ElGamal
Bogdan Warinschi from the University of Bristol, along with David Bernhard and Marc Fischlin, discusses the challenges in proving the chosen-ciphertext security of signed ElGamal encryption schemes. The potential solution involves adding a proof of knowledge to ciphertexts to prevent adversaries fro
3 views • 26 slides
Introduction to Cryptography: The Science of Secure Communication
Cryptography is the study of methods for sending and receiving secret messages securely. This lecture explores the application of number theory in computer science, focusing on the design of cryptosystems like public key cryptography and the RSA cryptosystem. The goal of cryptography is to ensure th
2 views • 53 slides
Overview of SMX Algorithm and AES Encryption Standard
The SMX Algorithm presents a fresh approach to the avalanche effect in the Advanced Encryption Standard (AES). Initially developed to overcome the limitations of the Data Encryption Standard (DES), AES boasts improved security and efficiency, supporting key lengths of 128, 192, and 256 bits. The AES
4 views • 19 slides
Block Ciphers in Cryptography
Explore the principles of block ciphers in modern cryptography, focusing on the Data Encryption Standard (DES) and its design principles. Learn about block cipher encryption, Feistel block cipher structure, n-bit block ciphers, ideal block ciphers, key length considerations, and challenges with idea
1 views • 44 slides
Encryption Techniques: From Transposition Ciphers to Rail Fence Ciphers
Explore the world of encryption techniques, diving into transposition ciphers and rail fence ciphers. Learn about encryption, decryption, plaintext, ciphertext, keys, and the art of secret writing. Discover how transposition ciphers reorder letters without changing their values and how rail fence ci
2 views • 26 slides
Cryptography Concepts and Encryption Methods Overview
Exploring elementary cryptography concepts such as encryption, cryptanalysis, symmetric and asymmetric encryption algorithms like DES, AES, and RSA. Delve into key exchange protocols, digital signatures, cryptographic hash functions, and the process of encryption and decryption in a cryptosystem.
5 views • 23 slides
Homomorphic Encryption Overview
Homomorphic encryption allows computation on encrypted data without revealing the underlying information. It enables secure delegation of data processing to a server while maintaining privacy. The process involves key generation, encryption, decryption, and evaluation of functions on encrypted data.
0 views • 40 slides
Bootstrapping in Fully Homomorphic Encryption
Fully Homomorphic Encryption (FHE) allows evaluation of unbounded-depth circuits without being limited by specific parameters. Bootstrapping is a critical technique to achieve full homomorphism by refreshing ciphertexts, enabling decryption functionalities within the encryption scheme. This process
4 views • 38 slides
Public Key Cryptosystems in RSA Encryption
Public key cryptosystems, like RSA, use two keys for encryption and decryption, with one key made public and the other kept secret. This asymmetric system allows secure communication, where the encryption key (E) is used to encrypt messages into ciphertext (C), which can only be decrypted back to th
2 views • 11 slides
Overview of Modern Cryptography and Data Encryption Standard (DES)
Exploring modern cryptography including symmetric key block ciphers, public key ciphers, stream ciphers, and post-quantum ciphers. Focus on Data Encryption Standard (DES), Simplified DES, Feistel cipher, key schedule, expansion function, S-Box, DES encryption, and decryption processes.
3 views • 37 slides
Cryptography Basics and Toolbox
Cryptography serves the goals of managing who can view data, ensuring data integrity, and verifying the origin of data. It involves dramatis personae like Alice, Bob, Eve, and Oscar. The toolbox includes hash functions, symmetric encryption, and asymmetric encryption. Hash functions play a crucial r
3 views • 32 slides
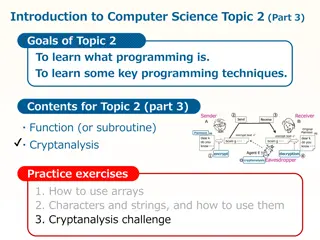
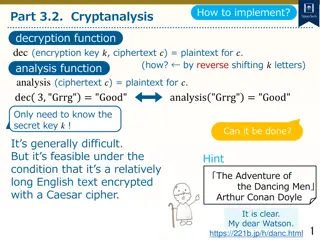
Cryptanalysis: Key Concepts and Techniques
Cryptanalysis is a fundamental aspect of cryptography that involves decoding encrypted communications and messages. This topic delves into the basic cryptographic tools, such as the Caesar cipher, and explores how encryption and decryption functions work. By understanding cryptanalysis, you can anal
2 views • 12 slides
Cryptanalysis and Decryption Techniques for Caesar Cipher
Learn how to decrypt Caesar cipher text using cryptanalysis techniques by analyzing letter frequencies and determining the secret key through character analysis. Explore methods to count character frequencies and find the most common letter to decipher encrypted messages.
4 views • 11 slides
Optical Security with Double Random Fractional Fourier Domain Encoding
Utilizing double random fractional Fourier domain encoding for optical security involves encryption and decryption methods based on the fractional Fourier transform of various orders, involving specific mathematical operations and notations. The process includes transforming the input function, encr
1 views • 13 slides
Spookily Homomorphic Encryption Explained
Spookily Homomorphic Encryption, as presented by Daniel Wichs based on joint works with other researchers, explores concepts like Fully Homomorphic Encryption (FHE) and Multi-Key FHE. It delves into the why, what, and how of FHE, with a focus on distributed decryption and achieving non-local relatio
4 views • 37 slides
Enhancing Python Programs with Comments and Programming Concepts
Understanding the importance of code readability through comments, Python programming concepts, conditional statements, and encryption/decryption. Explore tips for making code more readable, such as using booleans, if-elif-else statements, and while loops. Consider the significance of code appearanc
1 views • 80 slides
Cryptography and Symmetric Keys in Digital Communication
Cryptography, a vital part of digital communication, involves safeguarding messages from adversaries like eavesdroppers and impostors. Initially reliant on symmetric keys for encryption and decryption, the need to securely share keys posed a challenge. Technologies like DES and AES have advanced cry
2 views • 55 slides
Advanced Examples of Using Dictionaries and Lists in Python Programming
Explore more advanced techniques such as dictionary manipulation, list operations, pattern matching with regular expressions, and using simple programs to solve complex problems in Python programming. Discover methods like cryptanalysis, code breaking, frequency analysis, and rail fence decryption t
2 views • 22 slides
Fundamentals of Cryptography and Network Security
Explore the basics of cryptography, including classical encryption techniques, terminology definitions, types of encryption operations, cryptanalysis objectives and attacks, and the concept of cipher strength. Uncover the principles and methods behind encryption and decryption, key distinctions betw
1 views • 52 slides
Introduction to Traditional Ciphers: Columnar Transpositions
Traditional ciphers such as Columnar Transpositions involve rearranging plaintext letters based on a fixed number of columns. This technique enhances security by incorporating a keyword for encryption and decryption. Learn about the process and examples of implementing Columnar Transpositions in thi
2 views • 8 slides
Cryptology System Design Fundamentals - RSA Public Key System Analysis
The RSA public key system analysis involves determining suitable public and secret keys for users A and B, calculating distinct possible public keys, decrypting cryptograms, generating digital signatures, and discussing data ranges for secure communication. The solution covers the key generation pro
1 views • 16 slides
Cryptology System Design Fundamentals: ARSA Cryptosystem Examination Solutions
The given content discusses the solution to an ARSA cryptosystem final examination design problem, involving the computation of public and secret keys for users A and B, encryption and signing of messages, and considerations for attacker interceptions and computations. The solution guides through th
0 views • 18 slides
Advanced Techniques in Multi-Party Computation
Explore cutting-edge methods in Multi-Party Computation (MPC), including leveraging Fully Homomorphic Encryption (FHE) for minimal round complexity, constructing MPC directly via FHE techniques, and simplifying multi-key FHE constructions for efficient decryption. Learn about key concepts such as di
3 views • 17 slides
Cryptanalysis and Rail Fence Cipher Decryption Methods
In this discussion, we explored cryptanalysis techniques and the decryption process of the rail fence cipher. By mapping text to random letter permutations, breaking ciphers through histograms, and analyzing letter frequency distributions, we delved into deciphering encrypted messages. The session h
1 views • 27 slides
Encryption, Decryption & Hashing Overview
This content delves into the intricate processes of encryption, decryption, and hashing for maintaining data confidentiality and security. From creating users to inserting data and using AES encryption, explore the fundamental concepts and practical applications in database management.
0 views • 10 slides
Introduction to Cryptography Principles & Techniques
Explore the fundamental concepts of cryptography, including classical ciphers, substitution techniques, Caesar's cipher decryption, cryptanalysis methods, and more. Learn how cryptographic keys and permutations play a crucial role in securing information and communication. Dive into the world of enc
1 views • 25 slides
Confidentiality Techniques: Encryption, Decryption, and Hashing
Learn how encryption, decryption, and hashing techniques can be utilized to ensure data confidentiality and security. Discover the importance of safeguarding sensitive information such as credit card numbers through encryption methods. Understand the role of symmetric and asymmetric key encryption i
2 views • 28 slides
Introduction to Cryptosystems and RSA Public Key Cryptosystem
Explore the fundamentals of cryptosystems, including encryption, decryption, and the RSA public key cryptosystem. Delve into the concept of secret codes, unforgeable signatures, and coin flipping on the phone. Understand the setup of receivers and the encryption and decryption processes involved in
3 views • 19 slides
RSA Algorithm: Key Generation, Encryption, Decryption
Learn about the RSA algorithm, including key generation, key distribution, encryption, and decryption processes. Explore how public and private keys are utilized for secure messaging. Discover the fundamental concepts and steps involved in RSA encryption and decryption.
1 views • 6 slides
ElGamal Cryptography: Basics and Security Considerations
Explore the fundamentals of ElGamal Cryptography, including the public-key encryption and signature systems, security considerations, historical background, and practical applications such as message encryption and decryption. Learn about the innovative use of arithmetic in GF(q) for encryption and
0 views • 22 slides
Polyalphabetic Substitution Ciphers: Complexity and Decryption Tricks
The world of polyalphabetic substitution ciphers offers a deeper level of complexity by utilizing multiple alphabets to enhance security. This method involves encrypting and decrypting messages using alternating cipher alphabets, challenging traditional frequency analysis techniques. Discover how en
3 views • 12 slides