Safeguarding Student Privacy in Educational Technology: A Comprehensive Guide
This brief overview covers essential topics such as student privacy, data protection, educational technology use, compliance with privacy regulations, and communication strategies. It delves into the risks associated with student data collection and sharing, emphasizes the importance of privacy prac
5 views • 42 slides
Dynamic Pricing Algorithms with Privacy Preservation in Personalized Decision Making
Explore the challenges of preserving privacy in dynamic personalized pricing algorithms for decision-making in business. The research focuses on nonparametric demand models and differential privacy to safeguard user data against various privacy attacks, addressing the growing concerns and the need f
3 views • 30 slides
Understanding VA Privacy Issues and Sensitive Information
Explore the complex landscape of VA privacy issues, including data relationships, sensitive personal information (SPI), personally identifiable information (PII), individually identifiable information (III), and individually identifiable health information (IIHI). Learn about the roles and responsib
0 views • 29 slides
Understanding Privacy in Information Security Training
Privacy awareness training is crucial, covering topics such as the definition of privacy, importance of privacy protection, Personally Identifiable Information (PII), and Sensitive PII. Discover why privacy is vital to maintaining public trust, preventing identity theft, and complying with laws. Lea
0 views • 55 slides
NCVHS Subcommittee on Privacy Comments on HIPAA Privacy Rule for Reproductive Health Care
NCVHS Subcommittee on Privacy, Confidentiality, and Security provided comments on the Notice of Proposed Rulemaking (NPRM) to modify the HIPAA Privacy Rule for reproductive health care privacy. The NPRM aims to address concerns post-Dobbs ruling, introducing new provisions for prohibited uses and di
0 views • 13 slides
Privacy-Preserving Analysis of Graph Structures
Explore the world of graph structures and differential privacy in data publishing networks, focusing on preserving privacy while releasing structural information about graphs. Differential privacy techniques such as edge privacy and subgraph counts are discussed in detail, highlighting the challenge
0 views • 20 slides
Understanding Data Governance and Data Privacy in Grade XII Data Science
Data governance in Grade XII Data Science Version 1.0 covers aspects like data quality, security, architecture, integration, and storage. Ethical guidelines emphasize integrity, honesty, and accountability in handling data. Data privacy ensures control over personal information collection and sharin
7 views • 44 slides
FMCSA Privacy Awareness Training Overview for 2022
Understanding the importance of privacy and Personally Identifiable Information (PII) in the context of the Federal Motor Carrier Safety Administration (FMCSA). The training covers topics such as the definition of privacy, why privacy is crucial, what constitutes PII, the significance of sensitive P
0 views • 55 slides
Understanding Data Privacy Laws and Regulations in Saudi Arabia
This content provides an overview of data privacy laws and regulations, focusing on the landscape of data protection laws, examples of comprehensive regulations like FIPPS and GDPR, and sector-specific laws in Saudi Arabia. It includes a homework assignment to explore Fair Information Practices Prin
0 views • 28 slides
Powering the Digital Economy: Regulatory Approaches to Securing Consumer Privacy, Trust, and Security
This session at the ITU-BTRC Asia-Pacific Regulators Roundtable explored various aspects of online privacy, trust, and security in the digital ecosystem. It delved into the importance of data protection, privacy laws, and regulations to ensure online security and trust. Discussions also revolved aro
1 views • 7 slides
Understanding Breach of Confidence and Privacy Rights in English Law
English law does not provide a specific right to privacy, but breach of confidence laws offer protection against unauthorized disclosure of private information. While there is no overarching invasion of privacy tort, legal controls exist to balance freedom of expression with respect for individual p
0 views • 18 slides
Privacy Considerations in Data Management for Data Science Lecture
This lecture covers topics on privacy in data management for data science, focusing on differential privacy, examples of sanitization methods, strawman definition, blending into a crowd concept, and clustering-based definitions for data privacy. It discusses safe data sanitization, distribution reve
0 views • 23 slides
Privacy-Aware Smart Buildings: Ensuring Privacy Policies and Preferences
Smart buildings equipped with IoT technology raise concerns about privacy. This research explores capturing, communicating, and enforcing privacy policies and preferences in smart buildings, addressing issues like data collection, user preferences, and policy enforcement based on FTC and OECD guidel
0 views • 24 slides
Data Privacy in Sharing Sensitive Information
Understanding the importance of data anonymization and privacy requirements in sharing data. Exploring methods like k-anonymization and issues such as data linkage attacks that compromise individual privacy. Highlighting real-life examples like the MA governor's data linkage incident and the Netflix
0 views • 38 slides
Understanding Data Anonymization in Data Privacy
This content delves into the critical concept of data anonymization in the realm of data privacy, exploring methods such as k-anonymization, l-diversity, and t-closeness to protect sensitive information while ensuring data utility. It highlights real-world examples of data linkage attacks and emphas
0 views • 37 slides
Privacy and Data Protection in the Digital Age
Bart van der Sloot, a Senior Researcher at Tilburg Institute for Law, Technology, and Society, specializes in Privacy and Big Data, focusing on issues such as internet intermediary liability, data protection, and internet regulation. With expertise in the General Data Protection Regulation, internat
0 views • 89 slides
Understanding the Privacy Paradox: Attitudes vs. Behaviors
Social scientists have identified a Privacy Paradox where individuals with strong privacy concerns may not always engage in behaviors that protect their privacy. While some studies show a discrepancy between attitudes and behaviors, others suggest that privacy-concerned individuals do employ privacy
0 views • 14 slides
Kansas Student Data Privacy Legislation Overview
Kansas Student Data Privacy legislation, including the KS Student Data Privacy Act, emphasizes restrictions on disclosing student data and outlines permissible disclosures, enforcement measures, and reporting requirements. KSDE plays a key role in overseeing data management practices to ensure compl
0 views • 13 slides
Understanding Big Data and Privacy Issues in Today's Society
Explore the intersection of big data and privacy through the insights of Bart van der Sloot. Delve into current privacy issues, the application of big data, legal frameworks, recent developments, and the challenges between big data and privacy protection. Gain knowledge from interactive debates, stu
0 views • 63 slides
Understanding Big Data: Privacy Implications and Social Impact
Big Data refers to the vast amount of data generated, collected, and analyzed by organizations using advanced technologies. This data, when processed at high speeds from various sources, poses challenges to privacy rights and data protection. Big Data can reveal general trends and correlations but a
0 views • 36 slides
Understanding Data Security and Privacy: An Overview of k-Anonymity, l-Diversity, t-Closeness, and Reconstruction Attacks
Delve into the realm of data security and privacy, exploring concepts such as k-Anonymity, l-Diversity, t-Closeness, and Reconstruction Attacks. Learn about the importance of privacy concerns, privacy-preserving data sharing, real threats of linking attacks, and specific instances like the GIC Incid
0 views • 44 slides
Consumer Privacy Rights and Regulations Act (CPRA) Overview
The Consumer Privacy Rights and Regulations Act (CPRA) addresses the asymmetry of information between consumers and businesses, aiming to empower consumers to control their personal data and ensure transparency and accountability in data use practices. It emphasizes the need for stronger laws to pro
0 views • 14 slides
The Importance of Privacy in the Media Landscape
Privacy is the right to be left alone and control unwanted publicity. It is a central ethical issue in mass media, with concerns over invasion by news, advertisers, government, and the internet. Conflicts arise in various scenarios, from data collection to job screening methods. The modern world is
0 views • 42 slides
PoSeID-on: Innovative Data Management Platform for Enhanced Privacy
PoSeID-on project develops a portable platform integrating Blockchain, Cloud, and Smart Contracts to empower users in managing personal data securely. Offering a Privacy Enhanced Dashboard and Risk Management Module, it enhances data control, privacy, and GDPR compliance. Users can track data transa
0 views • 5 slides
Understanding Privacy Rights in Europe: A Comprehensive Overview
This content delves into the common definitions of privacy and the constitutional protection of privacy in Europe. It explores the right to privacy in individual, company, and government contexts, as well as ways to analyze the correlation between individual rights and others' duties. The discussion
0 views • 25 slides
Understanding Breach of Confidence and Privacy Rights in Legal Context
The legal landscape regarding breach of confidence and privacy rights, especially in the context of English law and the European Convention on Human Rights, is complex and ever-evolving. While English law traditionally does not recognize a right to privacy, recent developments and landmark cases hav
0 views • 18 slides
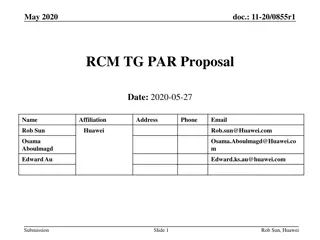
Proposal for IEEE 802.11 Privacy Enhancement
The proposal aims to enhance privacy in IEEE 802.11 standards by introducing mechanisms for data protection and compliance with privacy regulations. It focuses on safeguarding personal data from unauthorized access, processing, and sharing, while promoting ethical awareness of data usage. The projec
0 views • 5 slides
Online Privacy Concern in Post-Transition Era: A Study on European Internet Users
The study explores online privacy concerns among Internet users in Europe, focusing on countries in the post-transition era such as Croatia, FYR Macedonia, Serbia, and Bosnia and Herzegovina. Findings reveal growing discomfort with online profiling and data misuse, with significant variations based
0 views • 13 slides
Data Breaches and Privacy Concerns: An Overview
Privacy expert Marilyn Prosch, Ph.D., sheds light on the significant issue of privacy, emphasizing recent data breaches in various institutions and outlining some alarming cases where sensitive information was compromised. The incidents range from stolen laptops and office break-ins to mishandling o
0 views • 34 slides
Data Privacy Best Practices Training for Libraries
Explore a comprehensive data privacy training program for libraries led by Becky Yoose, a renowned Library Data Privacy Consultant. Supported by the U.S. Institute of Museum and Library Services, this training covers privacy fundamentals, current issues, risk assessment, vendor relations, patron pri
0 views • 33 slides
Enhancing Online Patron Privacy in Library Websites
This assessment by Marshall Breeding emphasizes the importance of maintaining online patron privacy on library websites. It covers key aspects such as the use of HTTPS, encryption, and privacy protection measures against vulnerabilities like tracking bots and unsecured transactions. The significance
0 views • 45 slides
Understanding Differential Privacy in Statistical Analysis
Gain insight into the concept of differential privacy in statistical analysis through key terminologies, foundational ideas, and practical examples. Explore the balance between data privacy and statistical quality, and learn how differential privacy serves as a mathematical guarantee to protect indi
1 views • 28 slides
Student Privacy Laws and Best Practices in Education Sector
Legislatures across various states are actively introducing and considering new student privacy laws, focusing on safeguarding online personal information and enhancing data transparency and security. Key themes include the introduction of privacy bills, the passing of data privacy laws, and the est
0 views • 30 slides
New Zealanders' Online Privacy Behaviours and Cyber Security Challenges
New Zealanders exhibit various online privacy behaviors in response to the age of big data, supported by strong privacy values. Different age groups demonstrate diverse strategies for managing online identity. While some benefit from economic prosperity and improved social outcomes, risks such as pr
0 views • 11 slides
Privacy Awareness Week 2017: Understanding the Australian Privacy Act
Explore the key aspects of the Australian Privacy Act 1988 during Privacy Awareness Week 2017. Learn about the Australian Privacy Principles, regulatory powers of the Commissioner, and the importance of managing personal information transparently. Discover how the Act covers sensitive information, t
1 views • 31 slides
Privacy Challenges in Online Social Networks
Online Social Networks (OSNs) like Facebook, Twitter, and LinkedIn have gained immense popularity with millions of users worldwide. However, these platforms present significant privacy issues, from protecting user data against unwanted exposure to the leakage of sensitive information. Challenges inc
0 views • 18 slides
The Challenges of Protecting Privacy with Differential Privacy
The article discusses the motivation behind using differential privacy to protect sensitive data while enabling useful queries. It highlights the promise of differential privacy, challenges faced, attacks on existing systems like PINQ and Airavat, and introduces a defense system called The Fuzz. The
0 views • 24 slides
Ensuring Privacy and Data Protection in the Digital Age
Privacy and Data Protection are essential in the digital age to safeguard individuals' rights and secure their information from unwarranted intrusion. This article discusses the importance of privacy, data security, and protection measures in the context of business, human rights, and legal framewor
0 views • 19 slides
Database Access Control & Privacy: A Common Ground Explored
Exploring the intersection of database access control and data privacy, this paper delves into the implications of data privacy concerns on Database Management Systems (DBMS). It discusses the need for more than just access control mechanisms and highlights the evolving landscape of data publishing,
0 views • 29 slides
Insights on Privacy and Security in Data Science and Cloud Computing
Explore key insights from Jon Crowcroft's talk at The Alan Turing Institute on privacy, security, data science, and cloud. Learn about layering, high throughput, low latency in data centers, decentralized IoT, community mesh networks, and the implications for privacy in data analysis. Discover how t
0 views • 15 slides