Cryptography,.Quantum-safe Cryptography& Quantum Cryptography
Dive into the world of cryptography, quantum-safe cryptography, and quantum technology as discussed in Maurizio D. Cina's presentation at CYBERDAYS in Prato. Topics include current cryptosystems, post-quantum cryptography, quantum key distribution, and future cryptosystems based on quantum algorithm
7 views • 17 slides
Security Threats and Public-Key Cryptosystems
Explore the world of security threats, passive and active attacks, and the importance of asymmetric encryption through the terminology related to asymmetric encryption, public-key cryptosystems, and public-key cryptography. Learn about the key components of public-key encryption schemes and the proc
2 views • 46 slides
Introduction to Cryptography: The Science of Secure Communication
Cryptography is the study of methods for sending and receiving secret messages securely. This lecture explores the application of number theory in computer science, focusing on the design of cryptosystems like public key cryptography and the RSA cryptosystem. The goal of cryptography is to ensure th
0 views • 53 slides
Introduction to Cryptography and Its Applications in Computer Science
Cryptography is the study of methods for sending and receiving secret messages. In this lecture, we explore the design and application of cryptosystems, such as the RSA cryptosystem and Turing's Code. The goal is to securely encrypt and decrypt messages using number theory to protect communication f
2 views • 53 slides
Public Key Cryptosystems in RSA Encryption
Public key cryptosystems, like RSA, use two keys for encryption and decryption, with one key made public and the other kept secret. This asymmetric system allows secure communication, where the encryption key (E) is used to encrypt messages into ciphertext (C), which can only be decrypted back to th
1 views • 11 slides
Limits on the Efficiency of Ring LWE-based Key Exchange
This study explores the limitations of Ring LWE-based key exchange protocols and their impact on non-interactive key exchange mechanisms. It discusses the LWE assumption, noise distribution, and the practical implications of small moduli q and noise-to-modulus ratio r. Additionally, it delves into P
0 views • 71 slides
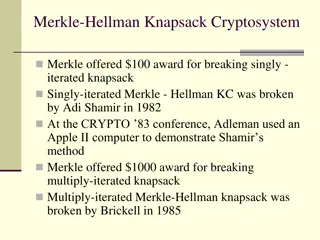
Overview of Knapsack Cryptosystems and Related Problems
The Merkle-Hellman knapsack cryptosystem is a cryptographic system that was initially proposed by Merkle, and later iterated versions were both broken by Shamir and Brickell in the early 1980s and 1985, respectively. This system is related to the classical knapsack problem, subset-sum problem, and e
0 views • 18 slides
Cryptographic Center in Novosibirsk: Advancements in Cryptography and Research
The Cryptographic Center in Novosibirsk, established in 2011, focuses on advancing cryptography through research, education, and international collaborations. With a team of researchers and students, the center explores various aspects of cryptography, including cryptographic Boolean functions, ciph
0 views • 33 slides
Securing Communication in the Quantum Computing Era
Embracing Post-Quantum Cryptography (PQC) is essential to counter the threat posed by large-scale quantum computers to current public key cryptosystems. Russ Housley, a prominent figure in the field, highlights the urgency to deploy PQC algorithms before a quantum computing breakthrough occurs. The
0 views • 9 slides
Symmetric Encryption and Basic Terminology
This content covers symmetric encryption techniques, substitution and transposition methods, rotor machines, and basic cryptographic terminology such as plaintext, ciphertext, cipher, and key. It also discusses the requirements and assumptions for secure symmetric encryption, and the model of symmet
0 views • 49 slides
Cryptography
Cryptography is the art of securing communication through the use of codes and ciphers. This overview covers fundamental concepts such as symmetric and asymmetric cryptography, hashes, attacks on cryptography, and best practices. Understand the terminologies in cryptography, the use of keys, and the
0 views • 63 slides
Public Key Cryptosystems and Digital Signature Algorithms
Symmetric and asymmetric encryption methods, disadvantages of symmetric encryption, Diffie-Hellman key exchange, and the importance of key distribution. Understanding the significance of public key encryption and its application in secure data communication.
0 views • 16 slides
Enhancing Gait Data Security Using Gray Code Quantization
This paper discusses techniques to improve the security of gait data in biometric cryptosystems by addressing issues such as low discriminability and high data variation. The proposed methods involve utilizing Linear Discriminant Analysis and Gray Code Quantization to enhance security and reduce fal
0 views • 25 slides
Web Applications Security Cryptography at TalTEch IT College
Learn about encryption and decryption functions, the use of keys in algorithms, breakable encryption, strong cryptosystems, and basic building blocks of encryption in web applications security cryptography at TalTEch IT College for the 2019-2020 Fall semester.
0 views • 40 slides
Classical Encryption Techniques and Cryptography Overview
Explore classical encryption techniques, symmetric cipher models, conventional cryptosystems, and the fundamental concepts of cryptography and cryptanalysis. Learn about plaintext, ciphertext, secret keys, and decryption algorithms in this comprehensive guide.
0 views • 22 slides
Lower Bound for Proving Hardness of Learning with Rounding
Explore the complexities of learning with rounding in cryptographic systems, including LWE and LWR problems, fundamental hardness assumptions, and constructions of deterministic cryptosystems. Can we directly construct pseudo-random functions from LWR? Delve into the challenges and implications in m
0 views • 92 slides
NIST Quantum-Resistant Cryptography Initiative
Explore the NIST PQC project focusing on quantum-resistant public key cryptosystems, monitoring quantum computing progress, and the timeline for introducing new cryptographic standards. Understand the urgency of transitioning to quantum-safe solutions to secure encryption in the face of evolving tec
0 views • 15 slides
Introduction to Cryptosystems and RSA Public Key Cryptosystem
Explore the fundamentals of cryptosystems, including encryption, decryption, and the RSA public key cryptosystem. Delve into the concept of secret codes, unforgeable signatures, and coin flipping on the phone. Understand the setup of receivers and the encryption and decryption processes involved in
0 views • 19 slides
Augmented Random Oracles and Hash Cryptosystems Overview
Explore the concept of augmented random oracles and the challenges in proving security in hash cryptosystems. Learn about the Random Oracle Model (ROM), its limitations, and efforts to design a model for improved security without instantiability issues. Dive into case studies like Encrypt-with-Hash
0 views • 25 slides
Introduction to Information Security - Prof. Kwangjo Kim Lectures & Course Overview
Dive into the world of information security with Professor Kwangjo Kim as he introduces fundamental concepts and cryptographic protocols. Explore various topics including classical ciphers, cryptosystems, and more to enhance your understanding of information security. Get ready to embark on a journe
0 views • 13 slides
Understanding Lattice Cryptanalysis for Cryptosystems
Dive into the comprehensive talk series on lattice cryptanalysis, covering topics like BKZ overview, mathematical tools, LWE attacks, and more, aimed at distributing expertise within NIST. Explore the intricate world of breaking lattice cryptosystems efficiently.
0 views • 36 slides