Cryptographic Reductions and Learning in Computational Complexity
This lecture explores the connection between computational complexity and cryptography, focusing on topics like pseudorandom functions, public-key cryptography, and learning from Gaussians. It delves into the implications of cryptographic reductions, lower bounds for learning MLPs, and the existence
3 views • 22 slides
Cryptographic Data Integrity Algorithms
Cryptographic data integrity algorithms ensure data integrity, verifying data received matches what was sent by authorized entities. Cryptographic hash functions play a crucial role in ensuring data integrity through hash values. Applications include message authentication, digital signatures, and v
7 views • 41 slides
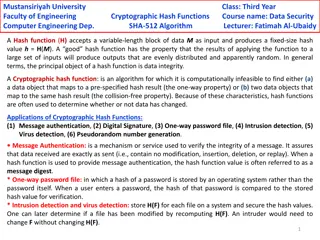
Cryptographic Hash Functions in Data Security: Mustansiriyah University Course Overview
Cryptographic hash functions play a crucial role in ensuring data integrity and security. This course at Mustansiriyah University's Faculty of Engineering covers the SHA-512 algorithm and its applications in various fields such as message authentication, digital signatures, and intrusion detection.
2 views • 6 slides
Diffie-Hellman Problems in Cryptography
Exploring Diffie-Hellman assumptions and problems including Computational Diffie-Hellman (CDH) and Decisional Diffie-Hellman (DDH). Discusses the difficulty of solving the DDH problem compared to CDH and discrete logarithm assumptions. Covers examples and implications of these cryptographic challeng
5 views • 6 slides
Security Goals and Cryptographic Algorithms
Introduction to security goals such as privacy, data integrity, authentication, authorization, and availability, along with the usage of cryptographic algorithms like symmetric and asymmetric key algorithms, keyed hashing, and digital signatures for achieving different security objectives in communi
2 views • 13 slides
Insights on Hardness Assumptions for Extreme PRGs
BPP=P requires certain complexity theoretical hardness assumptions. Recent advancements aim for extreme high-end PRGs based on stronger assumptions, presenting challenges in black-box proofing and loss factors. The cost of hybrid arguments for PRGs is analyzed, highlighting the need for qualitativel
3 views • 14 slides
Enhancing Cryptographic Key Generation with High-Quality Randomness
This presentation discusses the critical aspect of ensuring high-quality randomness in cryptographic key generation processes. It explores key vulnerabilities and common failure modes, emphasizing the importance of incorporating strong randomness. The content delves into various methods and issues r
2 views • 45 slides
Economic Models: Assumptions, Deductive Reasoning, and Logical Fallacies
Economic models utilize deductive reasoning to simplify real-world economic relationships. Assumptions vs. implications are key components, where assumptions reflect reality or are simplifying. This process helps identify conditions for specific outcomes to occur and distinguishes between consequent
6 views • 17 slides
Cryptographic Hash Functions
Cryptographic hash functions play a crucial role in various aspects of security, including integrity protection, checksum generation, password hashing, digital signatures, and more. They are designed to efficiently convert input data of arbitrary length into fixed-length output, aiding in tasks like
3 views • 32 slides
Enhancing Security for XMSS and SPHINCS+ Using Machine-Checked Methods
Advanced cryptographic techniques such as XMSS and SPHINCS+ are critical for ensuring secure digital signatures in a post-quantum world. This project focuses on improving the security and verification processes of XMSS and SPHINCS+ using machine-checked methods, aiming to enhance trust in these cruc
4 views • 17 slides
Cryptographic Algorithms and Hash Collisions Overview
Explore the world of cryptographic algorithms and hash collisions. Learn about various hashing algorithms like MD5, SHA-1, SHA-256, and more. Dive into the concepts of symmetric and asymmetric key algorithms and understand the risks associated with hash collisions. Discover the implications of post-
5 views • 58 slides
Franco-Japanese Cybersecurity Workshop Highlights and Future Plans
The 5th Franco-Japanese Cybersecurity Workshop concluded with insightful discussions on key areas such as IoT security, AI, hardware security, and supply chain security. The steering committee members shared plans for the 6th workshop in France, emphasizing policy discussions and cross-cutting issue
1 views • 18 slides
Quantum Computing and Its Impact on Cryptography
Quantum computing utilizes the principles of quantum mechanics to process information exponentially faster than classical computers. This advancement poses a significant threat to current cryptographic systems, especially those reliant on factors like RSA and Diffie-Hellman key exchange. If large-sc
4 views • 25 slides
Exploring the Role of Blockchain as a Trusted Third Party in Decentralized Systems
Blockchain technology serves as a decentralized and cryptographic Trusted Third Party (TTP) by enhancing trust, immutability, and censorship resistance in transactions. By distributing trust and utilizing cryptographic protocols, blockchain mitigates the need for a centralized authority, offering a
0 views • 30 slides
Cryptographic Center in Novosibirsk: Advancements in Cryptography and Research
The Cryptographic Center in Novosibirsk, established in 2011, focuses on advancing cryptography through research, education, and international collaborations. With a team of researchers and students, the center explores various aspects of cryptography, including cryptographic Boolean functions, ciph
2 views • 33 slides
Faster Implementation of Modular Exponentiation in JavaScript
Development of a cryptographic authentication toolkit for web application developers. Discusses modular exponentiation, digital signatures, elliptic curve cryptography, and the importance of DSA in providing secure authentication. Aims to offer both classical and elliptic curve cryptographic solutio
0 views • 22 slides
Zeroizing Attacks on Cryptographic Multilinear Maps: Overview and Applications
Cryptographic multilinear maps (MMAPs) enable computations on encoded secret data, offering similarities to fully homomorphic encryption (FHE) while providing distinct features. MMAPs find applications in identity-based encryption, non-interactive zero-knowledge proofs, and more. The evolution of MM
2 views • 45 slides
Cryptographic Protocols and Key Exchange
This content delves into the world of cryptographic protocols, discussing the importance of security measures such as symmetric cryptography, hash functions, and public-key cryptography. It explores the field's various studies, goals, Diffie-Hellman key exchange, and the significance of key size in
5 views • 28 slides
New Assumptions for Achieving Chosen Ciphertext Security in Cryptography
This research work focuses on presenting new assumptions for achieving chosen ciphertext security in public key encryption. The study aims to clarify the necessary and sufficient assumptions to realize general cryptographic primitives, particularly focusing on CCA secure PKE and KEM. The ultimate go
0 views • 27 slides
Scalable Cryptographic Authentication for High Performance Computing
This work discusses the scalable cryptographic authentication approach developed by Andrew Prout and team for high-performance computing. The LLGrid system architecture, challenges with interactive supercomputing, and utilization of LLGrid for various computing tasks are explored, highlighting the i
0 views • 34 slides
Assumptions in Genetic Twin Modeling: Technical and Interpretational Aspects
Genetic twin modeling involves making specific assumptions, some technical and others related to result interpretation. These assumptions, such as similar variances in MZ and DZ twins, play a crucial role in model estimation. Violations of these assumptions can lead to erroneous conclusions. Underst
16 views • 21 slides
MIT Foundations of Cryptography Lecture 22
In lecture 22 of MIT's Foundations of Cryptography series, delve into advanced cryptographic concepts and techniques. From modern encryption algorithms to cryptographic protocols, this lecture offers profound insights to enhance your cryptographic knowledge and understanding. Explore cutting-edge to
3 views • 46 slides
Security: An Overview of Cryptographic Techniques
Delve into the realm of cryptography with a comprehensive overview of techniques and protocols for ensuring secure communication channels. Explore the concepts of authentication, confidentiality, integrity, and availability. Uncover the tools and methodologies used in building cryptographic schemes
1 views • 26 slides
Cryptographic Signatures: Hash, RSA, and ECDSA Explained
In this content, the concepts of cryptographic signatures are explored, covering topics such as the hash and sign paradigm, the vulnerabilities of plain RSA signatures, RSA-FDH, and ECDSA (used in Bitcoin). The content delves into signature schemes, security definitions, threat models, and formal de
2 views • 38 slides
Hardness Assessment of Cryptographic Assumptions
Delve into the assessment of the hardness levels of cryptographic assumptions such as factoring-based and dlog-based problems. Understand the security recalls, algorithms for factoring, and dlog algorithms for generic and specific groups. Gain insights into the optimal algorithms and the efficiency
2 views • 5 slides
Concrete Parameters
In this presentation, we delve into the intricacies of cryptographic assumptions, specifically factoring-based and Dlog-based assumptions. We examine the complexity of these problems and the best possible algorithms for factoring and discrete logarithms. Understanding the algorithms for factoring an
3 views • 9 slides
Cryptographic Hashing
Cryptographic hashing is a key concept in data security, ensuring data integrity and authenticity. Learn about the properties of good cryptographic hashes, the difference between encryption and hashing, and delve into the specifics of SHA-1, its collisions, and processing of original messages. Under
0 views • 39 slides
Cryptographic Complexity of the Worst Functions Unveiled
Delve into the cryptographic complexity of the worst functions with expert insights from Amos Beimel, Yuval Ishai, Ranjit Kumaresan, and Eyal Kushilevitz. Explore the models, security considerations, and advancements in secure computation within information-theoretic frameworks. Understand the chall
2 views • 46 slides
Minimal Assumptions for Sender-Deniable Public Key Encryption
Explore the minimal assumptions required for sender-deniable public key encryption, delving into concepts like sender-deniable encryption, simulatable public key encryption, and the challenges of achieving deniability in cryptographic schemes from standard assumptions to non-black-box techniques.
4 views • 18 slides
Idealized Model for Cryptographic Primitives and Indifferentiability Framework
Explore new notions and constructions in public key crypto-systems, leakage resilience, related-key attack PKE, and idealized models for cryptographic primitives such as hash functions, random oracles, and more. Learn about the concept of Ideal NIKE and the Indifferentiability Framework in the conte
7 views • 20 slides
Cryptographic Techniques Overview
This overview explores cryptographic techniques, including cryptography, cryptographic protocols, key distribution, and the essentials of secure communication channels. It discusses the significance of authentication, confidentiality, integrity, and availability in maintaining secure channels. The c
3 views • 61 slides
NIST Cryptographic Standards Update and Project Progress
Learn about the progress and updates on the NIST Cryptographic Standards project, including the status of submissions, first-round candidates, and standardization guidelines for post-quantum cryptographic technology. Stay informed on the latest developments in cryptography from NIST.
3 views • 13 slides
MERS Experience Study and Assumptions
Discover the key aspects of the MERS Experience Study, including its goals, economic assumptions, and demographic considerations. Learn how updated economic assumptions impact contributions for FY 2021, and explore the importance of demographic assumptions for future planning. Stay informed on the c
4 views • 10 slides
Construction of Salsa20 and ChaCha Cryptographic Algorithms
This text discusses the construction and core functions of the Salsa20 and ChaCha cryptographic algorithms, highlighting their design principles, input parameters, and similarities in structure and operation. Salsa20, a family of flow-through cryptographic algorithms, was designed by Daniel J. Berns
2 views • 21 slides
Construction of Cryptographic Algorithms Salsa20 and ChaCha
This discussion delves into the construction of cryptographic algorithms Salsa20 and ChaCha, presenting insights into their designs, functions, and key components. Salsa20, part of the eSTREAM competition, is explored for its flow-through structure while ChaCha's unique composition and core function
0 views • 15 slides
Mitigating Multi-Target Attacks in Hash-Based Signatures
Explore research on mitigating multi-target attacks in hash-based signatures, including trapdoor identification schemes, hash-based signature schemes, and intractability assumptions in cryptographic hash functions. Gain insights into Merkle's hash-based signatures and minimizing security assumptions
0 views • 56 slides
Cryptographic Groups and Ideal Models Overview
Explore AGMOS, ideal models, and criticisms in the realm of cryptographic groups. Understand the significance of oblivious sampling and spurious knowledge assumptions in cryptographic design.
0 views • 15 slides
Building Non-Interactive Zero-Knowledge Proofs without Interaction
Learn about Non-Interactive Zero-Knowledge (NIZK) proofs based on Computational Diffie-Hellman assumptions, exploring completeness, soundness, and zero-knowledge properties. Discover the main question of how to construct NIZKs and the prior work behind it, including public-key assumptions and crypto
3 views • 29 slides
Understanding Cryptographic Hashing and SHA Algorithms
Discover the key concepts of cryptographic hashing, the properties of good cryptographic hashes, and insights into SHA algorithms such as SHA-1, SHA-2, and SHA-3. Learn about collisions, message padding, and the security features of SHA-256.
3 views • 39 slides
Understanding Cryptographic Hashing and SHA Algorithms
Explore the concepts of cryptographic hashing, the properties of good cryptographic hashes, and the significance of SHA (Secure Hash Algorithm) in ensuring data integrity and security. Learn about the distinction between encryption and hashing, the practical applications of cryptographic hashing, an
1 views • 38 slides