Line Segment Intersection
Geometric intersections play a crucial role in computational geometry for tasks such as solid modeling, collision detection in robotics, and overlaying subdivisions in geographic information systems. The problem of line segment intersection involves finding all intersection points between a set of c
0 views • 17 slides
Understanding 2D Collision Detection in Game Development
Explore the intricacies of 2D collision detection in game development through methods like distance checks, bounding shapes, and optimizing collision tests. Dive into concepts like sprite speed assumptions, square-square collisions, and rectangle testing complexities. Learn about useful Rectangle me
5 views • 29 slides
Chemical Kinetics: Understanding Reaction Rates and Factors
Chemical kinetics is a branch of physical chemistry that explores the velocity and factors influencing chemical reactions. It studies how reactants transform into products, considering conditions like temperature, pressure, and reactant concentrations. Factors affecting reaction rates include the na
7 views • 24 slides
Evolution of Mathematical Theories and Proof Systems
Development of mathematical theories such as model theory, proof theory, set theory, recursion theory, and computational complexity is discussed, starting from historical perspectives with Dedekind and Peano to Godel's theorems, recursion theory's golden age in the 1930s, and advancements in proof t
1 views • 29 slides
Psychological Theories of Criminality: Understanding the Roots
Psychological theories of criminality delve into the association between intelligence, personality, learning, and criminal behavior. Major theories include Psychodynamic Theory by Freud, Behavioral Theory by Bandura, and Cognitive Theory by Kohlberg. These theories explore how unconscious mental pro
1 views • 20 slides
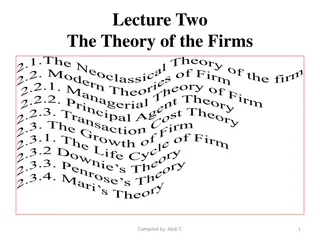
Understanding the Theory of Firms: Neoclassical vs. Modern Approaches
The theory of firms is explored through the Neoclassical and Modern perspectives. Neoclassical theory focuses on profit maximization, while Modern theory delves into managerial, principal-agent, and transaction cost theories. The discussion covers criticisms of Neoclassical theory and the essential
1 views • 79 slides
Spectrum Sensing for Enhanced Channel Access in Wireless Networks
This document presents a proposal for Spectrum Sensing Based Deferral (SSBD) to improve channel access in wireless networks. SSBD incorporates spectrum sensing with transmission deferral in a time-bound manner to enhance performance, reliability, and latency control. The proposed solution safeguards
1 views • 11 slides
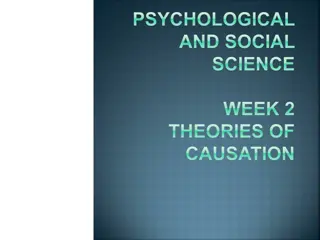
Theories of Causation in Psychological and Social Sciences
Overview of theories of causation categorized into psychological, social psychological, and sociological perspectives. Psychological theories focus on instinctive, biological, and psychological qualities of abusers, including Attachment Theory, Psychodynamic Theory, Social Learning Theory, and Situa
0 views • 15 slides
Understanding Political Theory through a Contextual Approach
Exploring G.H. Sabine's perspective on political theory through a contextual approach, emphasizing the importance of historical context and societal influences. Sabine argues that while political theory evolves with its contemporary politics, it should be analyzed within its specific time and social
0 views • 9 slides
Advanced Emergency Braking System (AEBS) Definition and Activation Guidelines
The provided content outlines the definition and activation requirements of the Advanced Emergency Braking System (AEBS). It covers the phases involved, including Collision Warning and Emergency Braking, as well as the speed limitations for activation. The system aims to automatically detect potenti
0 views • 12 slides
Evolution of Light Theory: From Wave Theory to Quantum Theory
At the turn of the century, the discovery of the photoelectric effect challenged the wave theory of light, leading to the development of the quantum theory by Max Planck and Albert Einstein. This new theory introduced the concept of discrete energy units known as quanta, bridging the gap between wav
1 views • 62 slides
Dp-branes, NS5-branes, U-duality, and M-Theory Overview
Overview of Dp-branes, NS5-branes, and U-duality derived from nonabelian (2,0) theory with Lie 3-algebra. Introduction to M-theory, including M2-branes and M5-branes in the strong coupling limit. Discussion on BLG theory, Lorentzian Lie 3-algebra, and the ABJM theory for M2-branes.
1 views • 32 slides
Understanding Time-Independent Perturbation Theory in Quantum Mechanics
Perturbation theory is a powerful tool in solving complex physical and mathematical problems approximately by adjusting solutions from a related problem with known solutions. This theory allows for more accurate approximate solutions by treating the difference as a small perturbation. An example inv
0 views • 19 slides
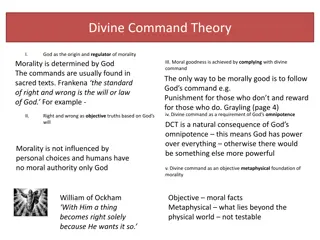
Ethical Theories: Divine Command vs. Virtue Theory Explained
Divine Command Theory asserts that morality is derived from God's commands, contrasting with Virtue Theory which focuses on developing moral virtues to achieve human flourishing and excellence. Divine Command Theory relies on religious texts, while Virtue Theory emphasizes the cultivation of virtues
0 views • 24 slides
Explore Biodiversity and Chemical Reactions Learning Resources
Dive into engaging resources covering biodiversity and chemical reactions, including BBC Bitesize links, educational videos, worksheets, and quizzes. Learn about food chains, sampling techniques, cycles, and concepts like collision theory and chemical changes. Access online platforms like BBC Bitesi
0 views • 23 slides
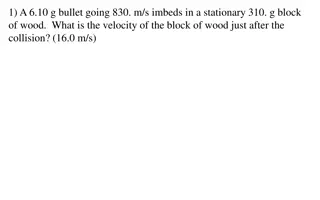
Physics Collision Problems Explained
Explore various collision scenarios involving bullets, blocks, cars, and people in this physics problem set. Calculate velocities, masses, and recoils to understand the dynamics of collisions and their effects on different objects involved.
0 views • 15 slides
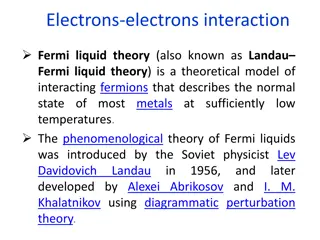
Understanding Fermi Liquid Theory in Interacting Fermion Systems
Fermi liquid theory, also known as Landau-Fermi liquid theory, is a theoretical model that describes the normal state of metals at low temperatures. Introduced by Landau and further developed by Abrikosov and Khalatnikov, this theory explains the similarities and differences between interacting ferm
0 views • 23 slides
Privacy Issues in IEEE 802.11 Networks: Tracking and MAC Randomization
This presentation delves into the privacy concerns surrounding 802.11 networks, focusing on tracking vulnerabilities and the limitations of MAC randomization in preventing tracking. It discusses the ease of tracking devices, the risk of passive tracking due to MAC addresses being visible in frames,
0 views • 27 slides
Understanding Chemical Kinetics and Equilibrium in Reactions
Explore the basic concepts of reaction rates, collision theory, activation energy, and energy diagrams in chemical kinetics and equilibrium. Learn how particles must collide with the correct orientation and enough energy to form an unstable activated complex. Discover the role of activation energy i
0 views • 24 slides
Computational Learning Theory: An Overview
Computational Learning Theory explores inductive learning algorithms that generate hypotheses from training sets, emphasizing the uncertainty of generalization. The theory introduces probabilities to measure correctness and certainty, addressing challenges in learning hidden concepts. Through exampl
0 views • 43 slides
Automata Theory and Theory of Computation Overview
This course overview covers concepts in automata theory and theory of computation, including formal language classes, grammars, recognizers, theorems in automata theory, decidability, and intractability of computational problems. The Chomsky hierarchy, interplay between computing components, modern-
0 views • 42 slides
Understanding the Dynamics of Collision: Bug vs. Windshield
Explore the intriguing physics behind a bug hitting a windshield, delving into concepts like Newton's third law, momentum conservation, and the differences in force, time of impact, and change in velocity. Discover why a bug goes splat while a windshield remains intact in a collision scenario, with
0 views • 19 slides
Theories of Interest in Microeconomics II
Explore various theories of interest in economics, including the Classical Theory, Liquidity Preference Theory by Keynes, Productivity Theory, Abstinence Theory, Time-Preference Theory, Fisher's Time Preference Theory, and the Loanable Fund Theory. These theories offer different perspectives on the
0 views • 6 slides
Exploring the Evolution of Atomic Theory
Delve into the historical journey of atomic theory starting from Democritus and Aristotle's views to modern advancements proving some aspects of Dalton's theory incorrect. Learn about key laws and theories such as the Particle Theory of Matter, Dalton's Atomic Theory, and JJ Thomson's discoveries, s
0 views • 30 slides
Drone Collision Avoidance Simulator for Autonomous Maneuvering
Our project focuses on developing a drone collision avoidance simulator using NEAT and Deep Reinforcement Learning techniques. We aim to create a model that can maneuver obstacles in a 2D environment, enhancing performance and survivability. Previous attempts utilizing non-machine learning solutions
0 views • 28 slides
Understanding Chemical Kinetics: The Rate of Reaction and Equilibria
Chemical kinetics explores the rate at which chemical reactions occur and the factors influencing them. This tutorial delves into the concepts of reaction rates, equilibrium, collision theory, and the role of concentration in determining reaction rates. By understanding these principles, industries
0 views • 117 slides
Understanding Rates of Chemical Reactions: Factors and Effects
Rates of chemical reactions are determined by the Collision Theory, which explains how reaction rates are influenced by factors such as concentration, surface area, temperature, catalysts, and stirring. Increasing concentrations, surface area, and temperature generally lead to faster reaction rates,
1 views • 8 slides
Understanding Chemical Kinetics: Reaction Rates and Activation Energy
Exploring the fundamental concepts of chemical kinetics, this content delves into reaction rates, collision theory, and activation energy in chemical reactions. It emphasizes the importance of particle collisions, correct orientation, and energy requirements for reactions to occur. Through energy di
0 views • 17 slides
Advanced Techniques in Collider Physics for Enhanced Luminosity
Explore cutting-edge research on beam-beam effects, crab waist colliders, and luminosity optimization in collider physics. Discover how innovative strategies like crab waist technology and bunch crabbing mitigation are revolutionizing particle collision studies. Dive into the complexities of achievi
0 views • 10 slides
Understanding the Relationship between Decisional Second-Preimage Resistance and Preimage Resistance in Cryptographic Hash Functions
This work delves into the subtle question of when Decisional Second-Preimage Resistance (SPR) implies Preimage Resistance (PRE) in hash functions. It presents a tool for enabling tight security proofs for hash-based signatures by exploring the success probability of adversaries against collision res
0 views • 25 slides
Foundations of Cryptography: Digital Signatures and Collision-Resistant Hash Functions
Foundations of Cryptography explores the construction of digital signature schemes and collision-resistant hash function families using one-way functions and safe primes. The content delves into the concept of collision-resistant hash functions and their construction from the discrete logarithm prob
0 views • 31 slides
Foundations of Cryptography: Lecture 12 - Digital Signatures and Collision-Resistant Hash Functions
The lecture covers the construction of collision-resistant hash functions from discrete log, the security behind it, and the implications for digital signature schemes. It delves into the theoretical foundations of cryptography, showcasing the interplay between one-way functions, hash functions, and
0 views • 25 slides
Comprehensive Overview of CSE 373 Data Structures and Algorithms Course - Autumn 2018
This document provides detailed information about the CSE 373 Data Structures and Algorithms course in Autumn 2018, presented by Shrirang (Shri) Mare. It covers topics such as hashing, collision strategies, hash tables, design decisions, testing, and more. The content includes announcements, midterm
0 views • 25 slides
Privacy Address Requirements for Wireless Personal Area Networks
This document discusses the privacy address requirements for IEEE P802.15 Working Group's TG4ab standard for Wireless Personal Area Networks (WPANs). It covers the need for 48-bit addresses with collision resistance, the use of different privacy addresses for each frame, and the adequacy of 12-bit c
0 views • 8 slides
Understanding TCAS - Traffic Collision Avoidance System
A Traffic Collision Avoidance System (TCAS) is a vital aircraft collision avoidance technology that helps reduce mid-air collisions by monitoring the airspace around an aircraft. TCAS operates independently of ground-based equipment and advises pilots on potential conflicting aircraft. Mandated by t
0 views • 13 slides
Vehicle Safety Protocols: Handling Tire Blows, Brake Failure, and More
Learn essential actions for handling emergencies like tire blowouts, brake failure, stuck accelerator, and steering failure. Additionally, understand off-road recovery, minimizing damage due to potholes, and escaping from a sinking vehicle. Discover collision avoidance techniques and steps to take i
0 views • 9 slides
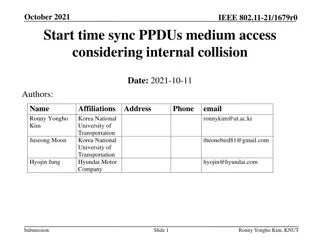
Understanding Start Time Sync Procedures in IEEE 802.11-21/1679r0
In the document authored by Ronny Yongho Kim et al., the focus is on start time sync PPDU medium access considering internal collision in IEEE 802.11-21/1679r0. It discusses the importance of defining a clear rule to resolve internal collision cases during medium access procedures. Specific attentio
0 views • 9 slides
Macromechanical Analysis of Lamina and Tsai-Hill Failure Theory Overview
The Tsai-Hill failure theory is based on the strengths of a unidirectional lamina, incorporating longitudinal and transverse tensile and compressive strengths, as well as in-plane shear strength. This theory, derived from the distortion energy theory, provides criteria for determining lamina failure
0 views • 15 slides
Understanding Hash Tables and Hashing Concepts in Computer Algorithms
This content delves into the concept of Hash Tables, covering topics such as the support for dictionary operations, achieving constant time through direct address tables, case studies in web server maintenance, and an exploration of hashing functions and collision avoidance. It also touches upon key
0 views • 40 slides
MitM Attack by Name Collision: Implications and Vulnerability Assessment
In this research study, the authors delve into the risks and vulnerabilities associated with Man-in-the-Middle (MitM) attacks exploiting name collision in the era of new generic Top-Level Domains (gTLDs). The study highlights how attackers can intercept web traffic by manipulating vulnerable domains
0 views • 25 slides