Circle of Security-Parenting: Enhancing Attachment for Child Development
The Circle of Security-Parenting program, an attachment-based intervention that supports children's mental health. Discover the benefits of secure attachment and understand the different types of insecure attachment. Find out how the program helps caregivers meet their child's attachment needs and r
31 views • 12 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Modern Perspectives on Attachment Theory: Bridging Research and Practice
Delve into the contemporary developments in attachment theory within social work and education. Explore how practitioners and researchers are navigating outdated notions and embracing newer insights to enhance their understanding and application of attachment concepts.
1 views • 16 slides
Understanding Autism Spectrum Disorder and Attachment: Insights from the Coventry Grid
Exploring the commonalities, desired outcomes, concerns leading to assessment, and the Coventry Grid regarding autism spectrum disorder and attachment. The Coventry Grid highlights the lack of flexibility of thought and behavior in individuals with ASD, emphasizing the importance of predictability,
0 views • 50 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Building Resilience and Changing Lives: Citizen Security and Justice Programme III
The Citizen Security and Justice Programme (CSJP) III by the Ministry of National Security focuses on enhancing citizen security and justice in Jamaica through various components such as culture change, community governance, labor market attachment, and employability. The program aims to build resil
1 views • 27 slides
Understanding Love Styles in Relationships Based on Attachment Theory
Early life experiences play a crucial role in shaping how we love in relationships. Milan and Kay Yerkovich have developed tools rooted in attachment theory to help individuals understand and improve their love styles. People tend to fall into five categories of Love Styles, such as the Avoider, who
1 views • 22 slides
Understanding Adenoviruses: Structure, Replication, and Epidemiology
Adenoviruses, known for causing respiratory infections, have at least 41 serotypes categorized into 6 subgenera. Their structure includes 252 capsomeres, 240 hexons, and specific proteins for attachment. The replication involves virus attachment, penetration, uncoating, and transportation of viral D
0 views • 22 slides
Understanding Sternberg's Triangular Theory of Love and Attachment Styles
Sternberg's Triangular Theory of Love defines the key dimensions of a healthy romantic relationship as intimacy, passion, and commitment. These components play vital roles in shaping relationships and can be influenced by attachment styles developed in infancy. Secure attachment leads to greater rel
1 views • 19 slides
Understanding Attachment, Trauma, and Life Stories in EMDR Therapy
Explore the impact of attachment-related trauma on adult attachment classifications, the significance of life stories in shaping our present, and how EMDR therapy helps individuals make sense of challenging childhood experiences to create a coherent narrative for healing and growth.
0 views • 66 slides
Understanding Infant Attachment Through the Strange Situation Experiment
The Strange Situation experiment conducted by Mary Ainsworth et al. in 1978 aimed to describe and evaluate the attachment relationship between caregivers and infants. The study involved observing caregiver-infant interactions through separations and reunions to classify attachment types such as secu
1 views • 6 slides
Understanding ARC: Attachment, Regulation, and Competency in Trauma Care
Explore the world of ARC (Attachment, Regulation, and Competency) in trauma care, a framework designed for working with children and teens affected by trauma. Learn about the core principles of ARC, its focus on strengthening relationships, enhancing self-regulation, and building resilience. Discove
0 views • 20 slides
Insights into Attachment Theory and Clinical Implications
Explore the clinical implications of attachment theory, as discussed by Miriam Steele and Bowlby, highlighting how early attachment patterns persist into adulthood and influence relationships. Learn about the Strange Situation test, Adult Attachment Interview, and intergenerational patterns of attac
0 views • 34 slides
Understanding Attachment Theory in Developmental Psychology
Attachment theory in developmental psychology, pioneered by Bowlby and Ainsworth, examines the emotional bonds between infants and caregivers. It delves into phases of attachment development, key components, and evaluation methods such as the Strange Situation Procedure. The theory emphasizes the si
0 views • 13 slides
Rochester Public Utilities Presentation on True-up of Attachment O Transmission Revenue Requirements
Rochester Public Utilities (RPU) holds annual meetings to discuss and provide information on the calculation of the True-up of RPU's 2016 Annual Transmission Revenue Requirements. The presentation also covers the True-up Adjustment applied to the 2018 Forward-Looking Rate. RPU uses a FERC-approved F
0 views • 14 slides
Looking for a Drill Saw Attachment? How Can It Transform Your Drill into a Power
If you're seeking versatility and efficiency in your toolkit, a drill saw attachment might be the perfect solution. This innovative accessory transforms your standard drill into a powerful cutting tool, allowing you to handle a range of tasks with ea
0 views • 4 slides
Looking for a Drill Saw Attachment? How Can It Transform Your Drill into a Power
If you're seeking versatility and efficiency in your toolkit, a drill saw attachment might be the perfect solution. This innovative accessory transforms your standard drill into a powerful cutting tool, allowing you to handle a range of tasks with ea
6 views • 4 slides
Attachment Wizard and File Management: A Comprehensive Guide for Efficient Workflows
Empower yourself with the knowledge and tools presented in this guide to effectively manage files, streamline attachments, and optimize your workflow. Discover best practices, learn about file naming conventions, explore different attachment methods, and enhance your productivity through expert tips
0 views • 12 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Understanding Canine Attachment and Cross-Species Relationships
Dogs exhibit strong social attachment to humans, forming enduring bonds that serve as a secure base. This attachment benefits both organisms, providing resources for survival and establishing social structures. Imprinting studies suggest that animals, like humans, develop proximity-seeking behaviors
0 views • 29 slides
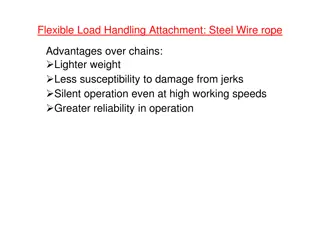
Understanding Wire Ropes for Flexible Load Handling Attachment
Wire ropes offer advantages over chains for flexible load handling attachment, such as lighter weight, less damage susceptibility from jerks, silent operation, and greater reliability. They consist of multiple wires or strands wound about an axis, with independent components interacting during servi
0 views • 17 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Understanding Therapeutic Parenting for Children with Trauma and Attachment Disruption
Therapeutic parenting is a child-centered approach tailored to address the complex emotional and behavioral needs of kinship, adopted, or permanent care children who have experienced attachment disruption and trauma. It focuses on nurturing, empathy, and building trust while refraining from conventi
0 views • 13 slides
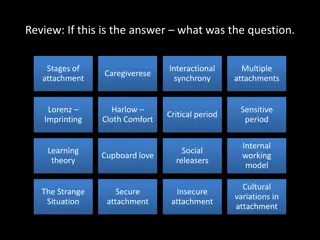
Understanding Bowlby's Attachment Theory: A Comprehensive Overview
This content provides an in-depth exploration of Bowlby's Attachment Theory, covering key concepts such as stages of attachment, interactional synchrony, multiple attachments, imprinting, secure and insecure attachment styles, and the impact of maternal deprivation. It also delves into short-term an
0 views • 22 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Understanding the Significance of Attachment in Supporting Vulnerable Children
Attachment plays a crucial role in the well-being of children, especially those in care. It influences their emotional and behavioral responses, impacting their overall development. This content emphasizes the importance of providing proper support and attachment relationships for children facing ad
0 views • 24 slides
Exploring the Nurture Group Approach and Attachment Theory
Delve into the Nurture Group Approach and Attachment Theory, examining the key ideas and theorists involved. Secure attachment and its evolutionary significance in fostering healthy relationships are highlighted. The importance of warm, continuous caregiver relationships in child development is emph
0 views • 29 slides
Understanding Attachment in Young Children and Caregivers
Attachment plays a crucial role in the development of young children, shaping their sense of security and emotional well-being. Secure relationships help children manage emotions and foster healthy identities, while insecure attachments may lead to behaviors like inhibition of exploration and diffic
0 views • 12 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Understanding Attachment Trauma and Healing Process
Attachment trauma involves disruptions in forming bonds, leading to complex trauma that affects neurological development. Therapy aims to create compassionate healing opportunities for individuals struggling with attachment-based trauma, addressing both big and little "t" traumas to increase emotion
0 views • 37 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides