Rational Expectations and the Efficient Market Hypothesis
The importance of expectations in various sectors and markets of the economy, including asset demand, risk and term structure of interest rates, asymmetric information and financial structure, financial innovation, bank management, money supply process, Federal Reserve, foreign exchange market, dema
6 views • 51 slides
Public key encryption, Digital signature and authentication
Understand the concept of public key encryption, asymmetric encryption, and the widely used RSA algorithm. Explore how public key cryptography revolutionized the field of encryption and its applications in confidentiality, authentication, and key distribution.
4 views • 12 slides
Ocean City Md Bike Week 2024 - bikesonline24.com
Ocean City Md Bike Week 2024, Maryland Bike Week promises to be an experience that both motorcycle enthusiasts and casual tourists won't soon forget. This event offers something for everyone, Home regardless of riding experience level. It's also a great way to have some high-energy fun. Let's explor
2 views • 4 slides
Understanding Security Threats and Public-Key Cryptosystems
Explore the world of security threats, passive and active attacks, and the importance of asymmetric encryption through the terminology related to asymmetric encryption, public-key cryptosystems, and public-key cryptography. Learn about the key components of public-key encryption schemes and the proc
0 views • 46 slides
Tamil Grade 2 Week 1 Alphabets and Numbers Learning Sessions
In this week's Tamil Grade 2 curriculum, students will engage in video sessions focusing on alphabets and numbers. The week begins with an alphabet video session followed by a revision session. Thursday features a numbers video session, and the week concludes with activities to write missing alphabe
0 views • 6 slides
Key Management and Distribution Techniques in Cryptography
In the realm of cryptography, effective key management and distribution are crucial for secure data exchange. This involves methods such as symmetric key distribution using symmetric or asymmetric encryption, as well as the distribution of public keys. The process typically includes establishing uni
1 views • 27 slides
Flashback in Four - Art and Techniques Exploration
Explore different aspects of art through Flashback in Four, incorporating Flashback Word of the Week, Artwork of the Week, and Technique of the Week. Delve into realism, highlights/shadows, negative image, and more, enhancing your understanding of various artistic concepts and methods. Immerse yours
1 views • 13 slides
Understanding Computer System Architectures
Computer systems can be categorized into single-processor and multiprocessor systems. Single-processor systems have one main CPU but may also contain special-purpose processors. Multiprocessor systems have multiple processors that share resources, offering advantages like increased throughput, econo
2 views • 25 slides
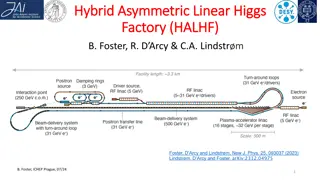
Innovative Hybrid Asymmetric Linear Higgs Factory (HALHF) Proposal
Cutting-edge proposal for the HALHF facility aiming to revolutionize particle acceleration technology by utilizing a hybrid asymmetric approach for electron-positron colliders. The design focuses on cost-efficiency and performance optimization, showcasing potential for significant advancements in hi
0 views • 18 slides
Overview of Cryptography Techniques and Algorithms
Exploring the diverse realm of cryptography, this chapter delves into both nonmathematical and mathematical encryption methods. It covers substitution and transposition ciphers, steganography, hybrid systems, hashing, symmetric algorithms like DES and AES, as well as asymmetric algorithms utilizing
7 views • 21 slides
Benefits of 8-Week Courses at Ivy Tech: A Comparative Study
Ivy Tech's 8-week course initiative, led by Dr. Cory Clasemann-Ryan, aims to increase student success through lower withdrawal rates. The white paper findings reveal that nationally, 8-week courses show higher success rates. Benefits include reduced burnout, continuous enrollment pathways, and facul
0 views • 12 slides
Old Palace Senior School Summer Menu Week One
The Old Palace Senior School Summer Menu for Week One offers a variety of delicious meal options for each day of the week, including Beef Mushroom Puff Pastry Pie, Roast Gammon with Gravy, Thai Style Green Chicken Curry, Battered Cod Fillet, Chicken Sausage with Wholegrain Mustard Gravy, and more. T
0 views • 7 slides
Fundamentals of Asymmetric Catalysis: Energetics and Principles
Exploring the principles and energetics of asymmetric catalysis, this study delves into the importance, classes of transformations, stereoselectivity, and transmission of asymmetry. It discusses reaction coordination diagrams, transition state stabilization, and the terminology of catalysis. The Cur
2 views • 20 slides
Fun-filled Moments in Unit 7 - A Week by Week Adventure
Immerse yourself in the adventurous escapades of Unit 7, where summer dreams, park visits, water park excursions, and school anecdotes come to life. Join the lively characters as they cherish sports, books, and language classes while reveling in the joy of pet companionship. Explore the engaging exp
0 views • 30 slides
Overview of Basic Security Properties and Cryptography Fundamentals
This content provides an introduction to basic security properties such as confidentiality, authenticity, integrity, availability, non-repudiation, and access control. It also covers the fundamentals of cryptography, including symmetric and asymmetric encryption, public-key cryptography, and the imp
0 views • 41 slides
Understanding Security Goals and Cryptographic Algorithms
Introduction to security goals such as privacy, data integrity, authentication, authorization, and availability, along with the usage of cryptographic algorithms like symmetric and asymmetric key algorithms, keyed hashing, and digital signatures for achieving different security objectives in communi
0 views • 13 slides
Primary School Autumn 2021 Lunch Menus: Week 1 & Week 2 Mains and Desserts
Discover the delicious lunch menus for autumn 2021 at the primary school, featuring a variety of mains such as cheese and tomato pizza, roast chicken, beef bolognese, and more. Indulge in mouth-watering desserts like raspberry ripple ice cream, secret brownie, lemon slice, and more. The menus offer
0 views • 4 slides
LAP Reading & Me: Six-Week Series with Kristi Sloan
Join Kristi Sloan, a K-2 LAP Reading Specialist, in a six-week series where she models reading skills with students and equips parents with tools to support their child's reading journey. The series includes activities like daily reading, letter sounds practice, sight words, hot and cold reads, joke
1 views • 17 slides
Daily ELA Review Grade 3 - Week 31 & Week 32 Activities
Engage your third-grade students with daily ELA review tasks for Week 31 & Week 32. Practice possessive pronouns, past tense, possessive nouns, verbs, adjectives, conjunctions, and more through interactive exercises.
0 views • 48 slides
Cryptography Concepts and Encryption Methods Overview
Exploring elementary cryptography concepts such as encryption, cryptanalysis, symmetric and asymmetric encryption algorithms like DES, AES, and RSA. Delve into key exchange protocols, digital signatures, cryptographic hash functions, and the process of encryption and decryption in a cryptosystem.
0 views • 23 slides
Understanding Silicon Detector Technology
Silicon is a remarkable material with low energy requirements for creating e-hole pairs, long mean free paths, high mobility for fast charge collection, and well-developed technology for fine lithography. Silicon detectors operate based on carrier band diagrams, density of states, and Fermi-Dirac di
0 views • 21 slides
Lasallian Heritage Week 2014 Event Recap
Lasallian Heritage Week 2014 was a week-long event celebrating the educational service to the poor in the Holy Presence of God. The week highlighted the history and values of the Institute, emphasizing solidarity, respect, and commitment to addressing poverty through education. Each day had specific
0 views • 7 slides
Understanding Public Key Cryptosystems in RSA Encryption
Public key cryptosystems, like RSA, use two keys for encryption and decryption, with one key made public and the other kept secret. This asymmetric system allows secure communication, where the encryption key (E) is used to encrypt messages into ciphertext (C), which can only be decrypted back to th
0 views • 11 slides
Key Distribution and Management in Cryptography
This presentation discusses key distribution and management in cryptography, covering symmetric and asymmetric key cryptography, methods for sharing symmetric and public keys, as well as key distribution techniques such as manual delivery, initial key distributions, and the use of trusted third part
0 views • 30 slides
Understanding the Role of Financial Institutions in the Global Economy
Explore the significance of financial institutions in facilitating the flow of funds from savers to productive investments, essential for a healthy economy. Delve into topics like transaction costs, asymmetric information, adverse selection, and moral hazard in the financial system, along with basic
0 views • 19 slides
Spring 2021 Flex Week Report Highlights
The Spring 2021 Flex Week Report highlights the successful workshops, enrollments, and feedback forms completed during the three-day event. Popular sessions on various topics were conducted via Zoom, with positive feedback from attendees. Insights from feedback and suggestions for the Fall Flex Week
0 views • 9 slides
The Physics of Supernovae and Neutron Stars
Explore the fascinating world of supernovae and neutron stars through historical postulations, Nobel Prize-worthy discoveries, multi-dimensional simulations, and paradigm shifts in understanding asymmetric supernovae. Dive into the complexities of core-collapse mechanisms, jet formations, and the po
0 views • 35 slides
Exploring Nuclear Symmetry Energy with QCD Sum Rule
This study delves into the concept of nuclear symmetry energy through the lens of QCD Sum Rule, discussing its implications in Rare Isotope Accelerator Plan and nucleon-nucleus scattering. Utilizing mean field approximation and Borel transformation, the research aims to understand asymmetric nuclear
0 views • 21 slides
4th Grade Math Daily Review - Week 1 and Week 2 Activities
Improve your 4th-grade math skills with daily review questions for Week 1 and Week 2. Practice multiplication, division, place value, rounding, factors, prime numbers, and more. Engaging activities including using area models, distributive property, finding remainders, listing multiples, and determi
0 views • 42 slides
Understanding Cryptography Basics and Toolbox
Cryptography serves the goals of managing who can view data, ensuring data integrity, and verifying the origin of data. It involves dramatis personae like Alice, Bob, Eve, and Oscar. The toolbox includes hash functions, symmetric encryption, and asymmetric encryption. Hash functions play a crucial r
0 views • 32 slides
Dynamic Core Boosting for Heterogeneous Computing
Exploring the challenges of workload heterogeneity in parallel programming, focusing on the impact of asymmetric hardware on performance and synchronization. Insights on modeling workload imbalance and boosting critical paths for efficient computation in heterogeneous multicores.
0 views • 22 slides
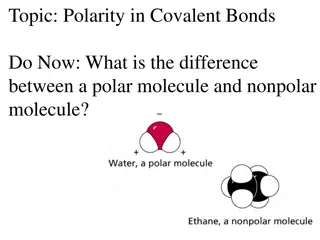
Understanding Polarity in Covalent Bonds
The difference between a polar molecule and a nonpolar molecule lies in the distribution of electrons. A polar molecule has an asymmetric electron distribution due to a significant difference in electronegativity, while a nonpolar molecule has a symmetric electron distribution. You can predict polar
0 views • 15 slides
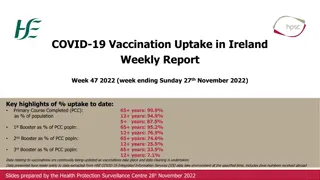
COVID-19 Vaccination Uptake in Ireland - Week 47, 2022 Report
The weekly report for Week 47, 2022 in Ireland shows the vaccination uptake percentages for Primary Course Completed (PCC), 1st Booster, 2nd Booster, and 3rd Booster across different age groups. As of Week 47, the vaccination rates vary among age groups, with the highest uptake seen in the 65+ years
0 views • 16 slides
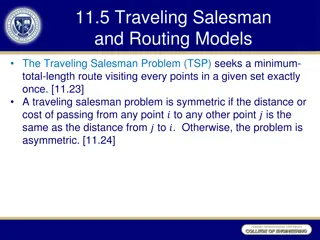
Understanding the Traveling Salesman Problem and Its Formulation
The Traveling Salesman Problem (TSP) is a classic optimization problem seeking the shortest route visiting a set of points exactly once. This involves symmetric and asymmetric cases, ILP models, subtours, and quadratic assignment formulations. By employing decision variables and constraints, optimal
0 views • 38 slides
Bank Loan Markups and Adverse Selection: Market Concentration Analysis
This research presentation by Beyhaghi, Fracassi, and Weitzner explores the impact of market concentration on bank loan markups and adverse selection. It delves into how asymmetric information across lenders influences interest rates in local banking markets, shedding light on the relationship betwe
0 views • 44 slides
Understanding Strong Asymmetric PAKE Protocols
Explore the intricacies of strong asymmetric PAKE (Password-Authenticated Key Exchange) protocols, including their security notions, possible attacks, and implementations. Learn about the challenges in constructing such protocols, the significance of universally composable security, and the limitati
0 views • 15 slides
Understanding Asymmetric Information and Externalities in Microeconomics
Explore the concepts of adverse selection, market inefficiency, signaling, and moral hazard arising from asymmetric information in microeconomics. Delve into scenarios like the Market for Lemons and health insurance to grasp how information deficiencies impact economic outcomes. Additionally, analyz
0 views • 22 slides
Insights into Persuasion and Equilibrium in Multidimensional Cheap Talk
Explore the dynamics of multidimensional cheap talk, focusing on sender-receiver interactions, influential equilibrium, welfare rankings, and fragility to asymmetries. Lessons touch on bubbling equilibrium, influential equilibrium issues, welfare rankings preferences, and the impact of asymmetric pr
0 views • 20 slides
Proposed Changes to School Week: Asymmetric Week Implementation
Proposed changes to the school week involve introducing an Asymmetric Week structure, with 4.5 days per week. This adjustment aims to modernize and enhance the educational provision in schools, with potential benefits for student health, well-being, and curriculum flexibility. The proposal is based
0 views • 14 slides
Java Programming Exercises Week 1 to Week 4 Solutions
Solutions and explanations for Java programming exercises from Week 1 to Week 4. Includes code fragments, explanations of Java variable names, calculations, error corrections, user input, and more.
0 views • 28 slides